Technical Analysis Reveals Connected Smart TV Security Risks
Executive Summary:
- Smart televisions manufactured by firms in the People’s Republic of China (PRC) present national security risks across three categories: intelligence and surveillance, denial and disruption, and influence and manipulation. Risk profiles vary significantly by service model and manufacturer.
- The degree of original equipment manufacturer (OEM) control over the device stack ranges from total (proprietary platforms like Hisense’s VIDAA) to partial but irreducible (platform partner models with Google, Amazon, or Roku), with the original design manufacturer (ODM) white-label model introducing an additional layer of supply chain opacity.
- Data collection through automatic content recognition, OEM telemetry, and ecosystem linkages is extensive, and data residency claims are frequently contradicted or left ambiguous by the manufacturers’ own privacy policies and technical infrastructure.
- The most consequential OEM capability is not data collection but the ability to modify device behavior at scale through over-the-air firmware updates, a privileged access point governed by engineering teams operating under PRC jurisdiction.
- PRC television manufacturers are expanding rapidly into adjacent smart home ecosystems, content services, and companion applications, transforming a discrete device risk into a persistent household-embedded data infrastructure whose complexity will grow increasingly difficult to govern.
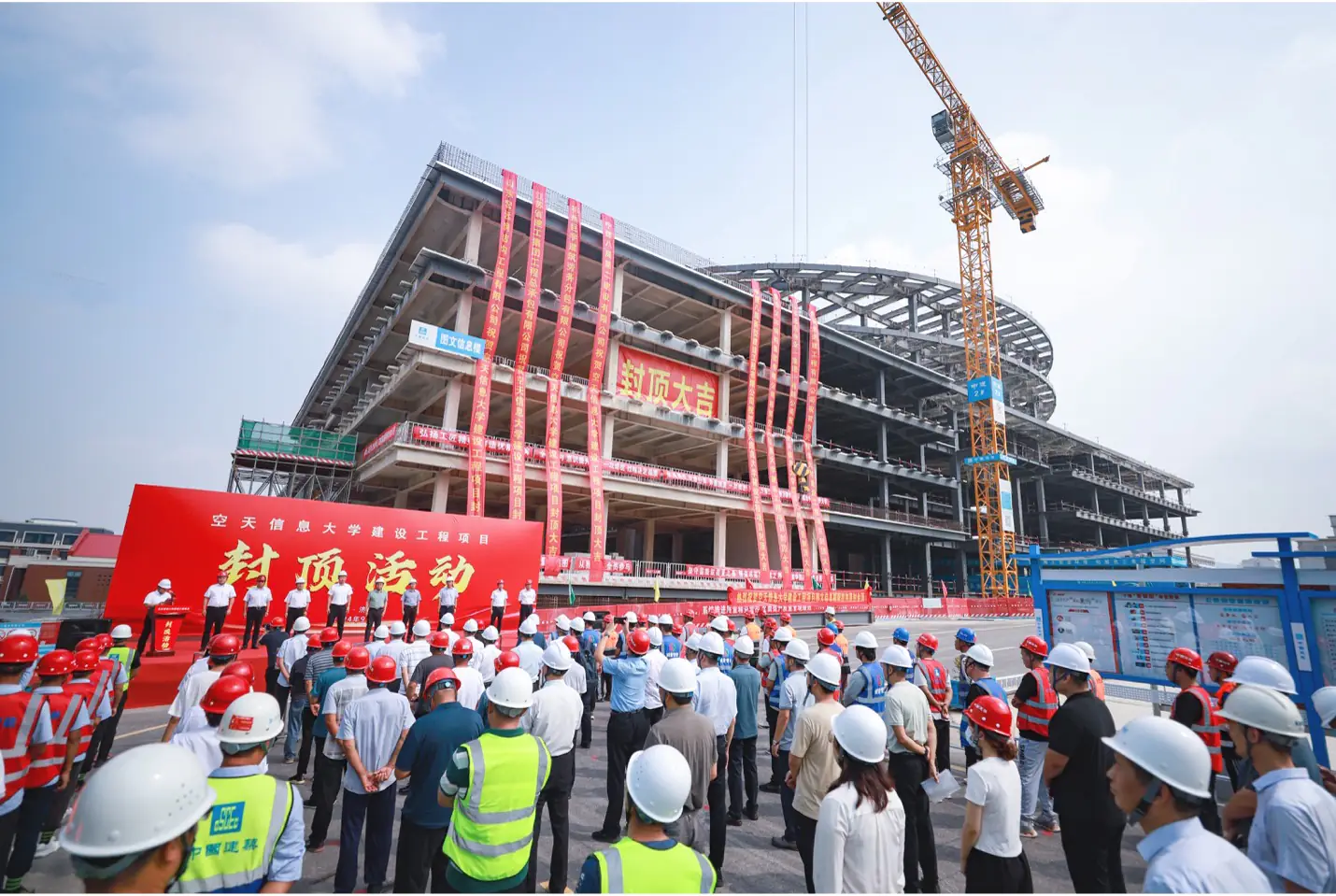
At the technology trade show CES 2025, Chinese firm Hisense unveiled an “Urban Governance Platform” alongside its consumer electronics lineup. The platform, built by Hisense TransTech, a subsidiary founded in 1998, uses proprietary artificial intelligence (AI) chipsets and big data analytics to optimize traffic flow, streamline public transit, manage disaster prevention, and coordinate public safety operations. It is already deployed across 169 Chinese cities: in Qingdao, train schedules automatically adjust during rush hour based on crowd monitoring, traffic lights adapt based on pedestrian flow detection, and bus routes optimize in real time (Hisense USA, December 18, 2024; Yanko Design, December 19, 2024).
The same company whose AI-powered surveillance and governance technology is embedded in the infrastructure of numerous Chinese cities is also one of the world’s largest television manufacturers. A state-owned enterprise operating under Qingdao’s state-owned assets supervision and administration commission (SASAC), Hisense sells internet-connected smart televisions to tens of millions of American households. These devices run proprietary software, collect behavioral data, and receive firmware updates from engineering teams in Qingdao. Hisense is not unique. Television manufacturers in the People’s Republic of China (PRC) have steadily extended their technical reach across the global TV market through acquisitions, licensing agreements, and original design manufacturer (ODM) relationships, often behind Western brand names.
The technical architecture of PRC-connected smart televisions may present risks to U.S. national security, even if these risks vary across manufacturers, service models, and device categories. The first three installments of this series built the case for examining these risks in layers. Part one documented the strategic policy cascade, from Premier Wen Jiabao’s (温家宝) 2009 designation of the “Internet of Things” (IoT) as a “strategic emerging industry” (战略性新兴产业) through to the 2024 notice by the Ministry of Industry and Information Technology (MIIT) on “Intelligent Connection of Everything” (万物智联), which has driven PRC dominance in global IoT manufacturing (China Brief, July 25, 2025). Part two mapped the policy toolkit: state-owned telecom networks, protected domestic markets, standards diplomacy, and Digital Silk Road infrastructure bundling (China Brief, August 7, 2025). Part three descended to the organizational level: CCP party cells embedded in every major manufacturer, Data Security Law (数据安全法) obligations requiring cooperation with state security, and specific documented vulnerabilities in devices manufactured by the firms TCL and Skyworth (China Brief, September 19, 2025). This fourth installment turns to the technical substrate: the device architecture, service models, data flows, and OEM capabilities that determine what these risks look like in practice.
A Framework for Connected Device Risk
Connected devices present three broad categories of national security risk. The first, intelligence and surveillance, involves the collection and exfiltration of data for espionage, behavioral profiling, or intelligence advantage. For smart TVs, this encompasses viewing habits captured through automatic content recognition (ACR), device fingerprints on local networks, voice recordings, app usage patterns, and household composition inferences derived from cross-device IP matching. The second, denial and disruption, involves degradation or manipulation of device function, ranging from individually bricking a device to coordinating firmware-level changes across large installed bases via over-the-air (OTA) update mechanisms. The third, influence and manipulation, involves shaping the information environment through content placement, factory-default app configurations, and preferential surfacing. This last category is less acute today, as content on smart TVs is largely dictated by third-party streaming apps. But it is growing more relevant as PRC manufacturers launch their own streaming services and content platforms.
These three risk categories do not operate in isolation. A device that collects household behavioral data (intelligence) could also serve as a vector for network disruption (denial) or as a platform for content manipulation (influence). And consequences cascade: a compromised smart TV affects not just the immediate user but the local network, linked smart home devices, and, at scale, potentially millions of households simultaneously. For consumer devices, these second order and aggregate consequences are where the real national security risk lies. But they are also the hardest to quantify.
Understanding where smart TVs fit in the broader landscape of connected devices is essential to assessing their risk profile. Connected devices exist on a spectrum. At one end sit commodity IoT products, such as thermostats, light bulbs, and basic sensors, with commoditized supply chains and minimal service-model complexity. At the other end are specialized systems like industrial control systems (ICS-SCADA) and telecom backbone equipment, with differentiated supply chains, known end-use environments, and consequence profiles that are visceral and quantifiable. Smart TVs occupy an uncomfortable middle ground. They have the service-model complexity of general-purpose computing devices, comprising multiple operating systems, app ecosystems, partner relationships, update pipelines, and advertising networks, but also the low-auditability and low-user-vigilance characteristics of commodity IoT. Consumers do not think of TVs as computers. They rarely check permissions, seldom update firmware manually, and do not run endpoint security software on them.
This distinction between scope-driven and scale-driven risk matters for policy. Specialized systems lend themselves to scope-driven assessment, which focuses on the consequences of a compromised device in a specific environment, evaluated against known operational contexts. The conventional ICTS risk assessment tooling, which includes entity lists, CFIUS review, and critical infrastructure frameworks, was designed for this mode. Consumer devices, by contrast, are scale-driven: supply chains are commoditized and opaque, there is no specific application context, and the primary drivers of consequences are market penetration, corporate and supply chain consolidation, and aggregate effect across all deployed devices. This is the analytical gap where smart TVs have been under-examined.
The analysis that follows applies two complementary lenses. The first is the adversary’s perspective, which focuses on intent, access, and capability; in other words, what a state actor wants to do, what legal and structural access it possesses, and what the technical architecture enables. The second is the defender’s perspective, which looks at threat, vulnerability, and consequence. Building on the preceding installments in this series, these are evaluated by examining devices’ technical architecture and assessing additional risks that scaling brings via market penetration.
Smart TV Technical Architecture and Risk Surface
A smart television is built in layers. At the base sits the hardware and firmware layer: the system-on-chip (SoC), flash storage, network interfaces, and the boot chain that sequences from ROM boot through bootloader and trusted execution environment to the operating system kernel. Above that is the operating system itself: Google TV, Amazon Fire TV, Roku OS, or a proprietary Linux-based platform like Hisense’s VIDAA or Skyworth’s Coolita. The middleware layer sits between the operating system (OS) and the user-facing applications, and includes media codecs, digital rights management, hardware abstraction, voice assistant integration, and, critically, the device management and telemetry services where original equipment manufacturer (OEM) data collection lives. The top layer is the application environment: app stores, runtimes, sandboxing, and update channels. Each layer has a different owner, and the boundaries between them define the risk surface.
What matters for risk assessment is not the layers themselves but who controls each one and under what governance framework. That question is answered not by the device’s brand or price point but by its service model. PRC-manufactured smart TVs generally follow one of three archetypes, each with a distinct risk profile.
- Proprietary OEM operating system: The manufacturer maintains control across every layer of the stack. Hisense’s VIDAA platform is the clearest example. VIDAA is a Linux-based OS developed, maintained, and governed entirely by Hisense (Spyro-soft, May 22, 2025). The company controls the boot chain, kernel, middleware, application store, update pipeline, and data collection services. There is no external platform partner providing independent audit, sandboxing governance, or update oversight. If Hisense, a state-owned enterprise, is directed or pressured to modify device behavior, there are no structural firebreaks in the software stack to prevent it. VIDAA is now the second-largest smart TV operating system globally, powering approximately 30 million televisions across more than 180 countries (NextTV, June 10, 2025). In the United States, Hisense deploys VIDAA on select models while using Google TV or Roku on others, a dual-stack strategy that complicates per-device risk assessment but does not eliminate VIDAA exposure.
- Platform-partner model: This model introduces meaningful structural boundaries. When TCL ships a Google TV, Google controls the operating system, app store, and core middleware, while TCL retains control over the hardware, firmware, bootloader, and a vendor-specific partition within the Android software build that includes the OEM’s telemetry, device management, and launcher customizations. Google’s Play Protect and verified boot concepts provide some assurance at the OS and app layers, and TCL’s vendor partition is approved during the certification process. But the extent of ongoing audit—what Google actually inspects in TCL’s vendor partition, how frequently, and with what rigor—is deal-specific and not publicly documented. Roku TV and Fire TV impose similar but not identical boundaries, with Roku generally retaining much tighter platform-level control and Fire TV governance varying by OEM agreement. The platform partner model reduces the OEM’s unilateral control over the software stack, but the firebreaks are partial: the OEM still controls the hardware and firmware layers beneath the platform, and its privileged middleware runs with elevated permissions on the device.
- ODM or “white-label” model: This model introduces a much different kind of product and branding opacity. Tongfang (同方), a Tsinghua University spin-off now 21 percent owned by China National Nuclear Corporation, the state-owned enterprise in charge of the country’s civilian and military nuclear programs, manufactures televisions sold under the Westinghouse, Element, and formerly Seiki brand names (VentureBeat, January 3, 2017; MarketScreener, accessed February 20). When those devices run Amazon’s Fire TV, the platform controls most of the software stack and consumer data flows terminate at Amazon, not Tongfang. But Tongfang designed the hardware, including SoC selection, board layout, network interfaces, and low-level firmware. that provenance is invisible to the consumer. A shopper buying an Element TV at Walmart has no indication that the device was designed and manufactured by a SASAC-affiliated Chinese state enterprise.
Table 1: Per-Manufacturer Technical Summary
| Manufacturer | OS Families | Service Model | OEM Control | Key Risk Factor |
| TCL | Google TV, Roku TV, Fire TV | Multi-platform portfolio | Medium–High (varies) | Largest global market share growth; multi-OS strategy means risk is segment-specific |
| Hisense | VIDAA (proprietary), Google TV | Dual-stack: proprietary + partner | High (VIDAA) / Medium (Android) | VIDAA gives full OEM control; #2 global smart TV OS |
| Skyworth | Coolita/Coocaa (domestic), Google TV (export) | Split by market | High (domestic) / Medium (export) | Explicit PRC access to data stored in India/Germany |
| TongFang | Fire TV, customer-specific | ODM integrator | Low (software) / High (hardware) | Brand opacity: consumer unaware of CNNC-affiliated manufacturer |
Sources: Spyro-soft, 2025 (VIDAA architecture); NextTV, 2025 (VIDAA market share); MarketScreener, 2019 (TongFang/CNNC ownership); VentureBeat, January 3, 2017 (Fire TV Edition brands); Coolita Privacy Policy (Skyworth data access); Texas Attorney General, December 15, 2025.
The common thread across all three archetypes is that the OEM—or, in the ODM case, the hardware integrator—retains some irreducible level of control. Even in the most constrained platform–partner arrangement, the manufacturer controls the physical device, the boot chain, and at least some privileged firmware. Given this fact, key questions for consideration must answer how deep such access runs, what governance measures constrain it, what is visible to partners and end-users, and what degree anyone outside the manufacturer is in a position to audit or verify claims.
Data Collection, Storage, and Access
Smart TVs collect data through three overlapping channels. The first and most scrutinized is automatic content recognition (ACR), a technology that captures what is displayed on screen and matches it against content databases to identify viewing behavior. TCL deploys ACR through a partnership with Samba TV, a privately held U.S. company whose technology is integrated at the chipset level across 24 smart TV brands and claims reach into 111 million American households (Samba TV, January 5, 2023, accessed February 19). Hisense deploys ACR through an exclusive global partnership with Nexxen (formerly Tremor International), renewed in August 2025 through at least 2029, which grants Nexxen direct access to viewing data collected through the VIDAA platform (GlobeNewsWire, October 26, 2021; Nexxen IR, August 11, 2025). Hisense’s own Enhanced Viewing Service privacy notice names Nexxen as the ACR provider and describes how ACR-derived analytics can target advertisements on “other devices” sharing a household IP address (Hisense USA, March 1, 2025). Skyworth’s former ACR partner, Gozen Data (勾正数据), a Beijing-based firm, went further: its software scanned local networks every ten minutes, collecting not just viewing data but device names, IP addresses, network interface identifiers, and the names of nearby WiFi networks—well beyond the television itself (The Register, May 4, 2021; EDN China, April 28, 2021). Skyworth terminated the partnership in May 2021 after public disclosure, but the incident illustrates how third-party data services embedded in smart TVs can operate well outside their stated scope. The second channel is OEM telemetry: device diagnostics, app usage, network environment data, and crash reports collected by privileged, pre-installed applications that the user typically cannot remove. The third is ecosystem data. Hisense’s privacy policy, for instance, explicitly describes using ACR-derived analytics to target advertisements on “other devices” sharing a household IP address, extending the television’s data collection surface to phones, tablets, and laptops in the home.
Where that data resides—and who can access it—is much harder to pin down than it should be. Privacy policies and infrastructure evidence tell different stories depending on the company, the product line, and the vintage of the policy. Hisense’s current U.S. Data Protection Policy states that its servers are “currently located in the United States of America,” and DNS analysis confirms at least some infrastructure resolves to Amazon Web Services in Oregon (Hisense USA, April 30, 2023). But an older Hisense smart TV policy that is still within the lifecycle of devices in consumer homes explicitly permitted transfer of personal information to the PRC (Hisense USA, January 1, 2020). TCL’s global smart TV privacy notice reserves the right to “transfer, storage and process your information within and outside of your country,” while its corporate privacy policy states that personal data “will be transferred and stored in Mainland China” (TCL Tech, October 15, 2024). Skyworth’s Coolita OS policy is unusually transparent: cloud services are deployed in India and Germany, but “maintenance operations in China may access” data stored in those locations. This represents an explicit PRC access pathway regardless of where primary storage sits (Coolita, 2021).
Table 2: Data Residency Risk Summary
| OEM | Privacy Policy Language | Infrastructure Evidence | PRC Access | Risk Level |
| Hisense | Current: “servers currently located in the United States.” Older policy: permitted PRC transfer. | mytv.hisense.com → AWS ELB (us-west-2) | Documented in older policy | High |
| TCL | TV: “transfer…within and outside of your country.” Corporate: “stored in Mainland China.” | leiniao.com → Google Cloud; TCL Channel → AWS S3 (us-west-1) | Explicit in corporate policy | High |
| Skyworth | Cloud in India/Germany; “maintenance operations in China may access.” | Coolita OS cloud services | Explicit operational access | Medium–High |
| TongFang | No consumer TV privacy policy found. ODM model: data flows to platform OS. | EU enforcement: employee data on PRC servers | Uncertain | Medium (opaque) |
Sources: Hisense USA Data Protection Policy; Hisense Data Protection Policy (2020); TCL Tech Privacy Policy; TCL Global Privacy Notice; Coolita Privacy Policy; ViewDNS (DNS evidence); JDSupra (EU enforcement, TongFang).
The practical reality is that corporate domicile alone is an unreliable indicator of data residency. More actionable signals include named partners in privacy notices, service hostnames embedded in firmware and applications, and where those hostnames resolve, such as their cloud provider, geographic region, and network owner. This kind of infrastructure-level analysis reveals that even when a manufacturer claims U.S.-based hosting, the policy language often reserves broad cross-border transfer rights, and the specific location of consumer telemetry databases frequently goes unspecified. The gap between what privacy policies say and what the technical infrastructure does is itself a risk factor. And for PRC-connected manufacturers operating under article 35 of the Data Security Law (数据安全法) and article 7 of the National Intelligence Law (国家情报法), that gap takes on a different character than it would for a Western company with similar ambiguity. Deeper questions, such as the full scope of data collected, the infrastructure supporting its storage and processing, internal retention and sharing practices, and the identity of all downstream recipients, can ultimately only be answered by the companies themselves. This is where governments typically step in, whether through subpoena authority in the context of a national security investigation or a CFIUS transaction review. Absent a law requiring detailed disclosure of data collection, retention, use, and sale as a condition of participation in the U.S. market, the burden of discovery rests entirely on investigative authorities, an approach that is inherently reactive and limited to the cases that happen to attract scrutiny.
The Scale Problem
Smart televisions occupy an uncomfortable position in the national security landscape. They are not the specialized, scope-driven systems (like telecom backbone equipment, industrial control systems, or military platforms) that conventionally attract threat assessment and mitigation. High-profile devices in the most sensitive environments tend to receive the most attention, and for good reason: each compromised device in those contexts can produce outsized, cascading consequences, and the line separating tolerable risk from unacceptable exposure is comparatively clear. Defending critical infrastructure against supply chain compromise is a challenging but tractable problem—one that existing authorities like the Covered List published by the Federal Communications Commission (FCC), the Department of Defense’s list of Chinese military companies (the CMC list), FASC, ICTS, and others are at least in part intended to address. Other, more outbound programs like the Commerce Department’s Entity List can relieve some supply chain pressure in the long run, but do little to address dependence at home. Still, though, each of these programs only prohibit and constrain when a national security risk presents itself, at which point a commodity product has already achieved the market share and ecosystem diversity that makes its removal difficult and costly. There are few measures to shape these companies and their offerings as requirement of market participation.
Commodity consumer devices present the inverse problem. The risk scope of any individual smart television is small. No single compromised TV in a suburban household is likely to produce a national security crisis. But smart TVs are not assessed individually—they are deployed at scale, across tens of millions of households, collecting behavioral data, receiving firmware updates, and integrating into expanding ecosystems of connected devices. The risk is measured in the aggregate: a composite net exposure where each device contributes a small quantum of intelligence value, surveillance access, or disruption potential that, summed across an installed base of this size, becomes unfathomably large. And the televisions themselves are only part of the picture. The companies that manufacture them are building outward, expanding into adjacent smart home ecosystems, content platforms, and companion applications, while simultaneously growing their market share through channels that attract little public scrutiny: OEM licensing agreements, white-label partnerships, and ODM arrangements that embed PRC-engineered software stacks in devices sold under other brands. The scale grows, largely in silence.
At the core of this challenge is an uncomfortable asymmetry. Not every Chinese company is a national security threat, but any Chinese company could become one. This probability increases as a firm’s market share, privileged access to user data, and potential usefulness as an intelligence asset grow. PRC law does not permit the kind of refusal or disclosure that would allow external observers to distinguish between a manufacturer that has been co-opted and one that has not—and no independent judiciary exists to check legal or operational overreach by state authorities. This is not a statement about intent; it is a structural observation about the legal and political environment in which these companies operate. Unfortunately, it is precisely the scale and market penetration that make these firms strategically significant that also makes a ban or “rip and replace” approach practically difficult or cost-prohibitive. The fifth and final installment in this series will examine the shifting risk dynamics of the smart television ecosystem—OEM capabilities, supply chain opacity, regulatory gaps, and the expansion trajectory that is transforming a bounded device-level risk into an open-ended one—and consider key challenges and considerations for governing it.