
Internet Censorship Tools Exported Along Belt and Road
Executive Summary:
- Over 600-gigabytes of leaked documents illuminate the connections between the People’s Republic of China’s (PRC) Mesa Laboratory and the firm Geedge Networks. The documents show implementation of Geedge’s technology outside of the PRC, including in Ethiopia, Pakistan, Myanmar, and Kazakhstan.
- Technology transfers follow the Digital Silk Road and occur between the PRC and One Belt One Road (OBOR) initiative partners. This follows the PRC’s stated goals of enhancing digital infrastructure and data governance cooperation with OBOR countries.
- Leaked data shows that Geedge does not exclusively utilize proprietary code, instead using existing commercial software development kits (SDKs) and open-source components. This could potentially raise legal concerns among developers.
In mid-November, the artificial intelligence (AI) firm Anthropic disclosed the first publicly documented case of a near end-to-end espionage operation orchestrated through a commercial AI coding assistant. The company claimed that a state-linked actor in the People’s Republic of China (PRC) had weaponized its Claude Code tool to automate elements of a cyber-espionage campaign targeting dozens of governments, defense firms, and technology companies worldwide (Anthropic, November 14). The attackers used the large language model to script malware, generate spear-phishing lures, and optimize software infrastructure. U.S. lawmakers responded by summoning Anthropic’s CEO to testify on AI-enabled cyber threats (Cyberscoop, November 26).
The model of state-linked commercial actors supporting the PRC’s hitherto unique approach to Internet governance is now moving overseas. A tranche of documents leaked in September 2025 show that Beijing is systematically equipping foreign governments to replicate and innovate its authoritarian Internet governance model. The materials, consisting of source code, field-test reports, project management software tickets, and internal briefings, reveal how Beijing’s Great Firewall is being packaged and exported as turnkey infrastructure to One Belt One Road (OBOR) initiative and Digital Silk Road partner countries. [1]
The 600-gigabyte tranche is the largest leak to date of internal documents relating to the Great Firewall (Great Firewall Report, September 12). It exposes the relationship between the PRC firm Geedge Networks (积至信息) and MESA Laboratory, which is under the Chinese Academy of Science’s Institute of Information Engineering. [2] Earlier research, such as analysis of files leaked from the Shanghai-based hacking contractor iS00n, focused on how the PRC monitors and penetrates its partners’ networks (China Brief, March 29, 2024, December 20, 2024). This latest dump provides insight on how partner countries seek to acquire and adapt Beijing’s repressive apparatus for themselves. [3]
From Domestic Firewall to Exportable Product
The Geedge and MESA documents show that the PRC’s system for domestic Internet control has been broken down into exportable components that are being sold as commercial products. At its core is the Tiangou Secure Gateway, a device that can be installed at major telecom operators to scan, filter, or block almost all Internet traffic in a country. On top of this, software modules known as Cyber Narrator and TSG Galaxy enable security agencies to run queries regarding virtual private network (VPN) users, and issue new blocking or monitoring rules based on those results.
Geedge has launched pilots and deployments abroad in Ethiopia, Pakistan, Myanmar, and Kazakhstan, as well as in PRC regions and provinces such as Xinjiang and Fujian. The company’s international clients have long records of surveillance and censorship; what the leaked documents show is that PRC technology is now being used to enhance their capabilities (InterSecLab, September 9). Once a government adopts the platform, new features can be rolled out through software updates, allowing foreign clients to “inherit” capabilities first tested and finetuned inside the PRC.
Exporting the logic of the PRC’s Great Firewall has normative consequences. When governments in Myanmar or Ethiopia adopt Geedge’s stack, they are not just acquiring a product; they are aligning their concept of “normal” Internet governance with that of Beijing. A key part of that concept is deep packet inspection (DPI). DPI is a technology that allows operators to examine data packets and see which websites or IP addresses users are connecting to, as well as analyze the content and patterns of their traffic in real time. It allows authorities to identify specific applications (such as VPNs, Tor or messaging apps), monitor who is using them and, if desired, block or degrade those connections. It is a key censorship technology that, in the PRC, is associated with privacy infringement (Yang, 2015; Li, March 3; ChinaFile, accessed December 4). [4] For Beijing, DPIs are deployed as routine infrastructure and behavior-based blocking is a standard security function.
Figure 1: Cyber Narrator Dashboard
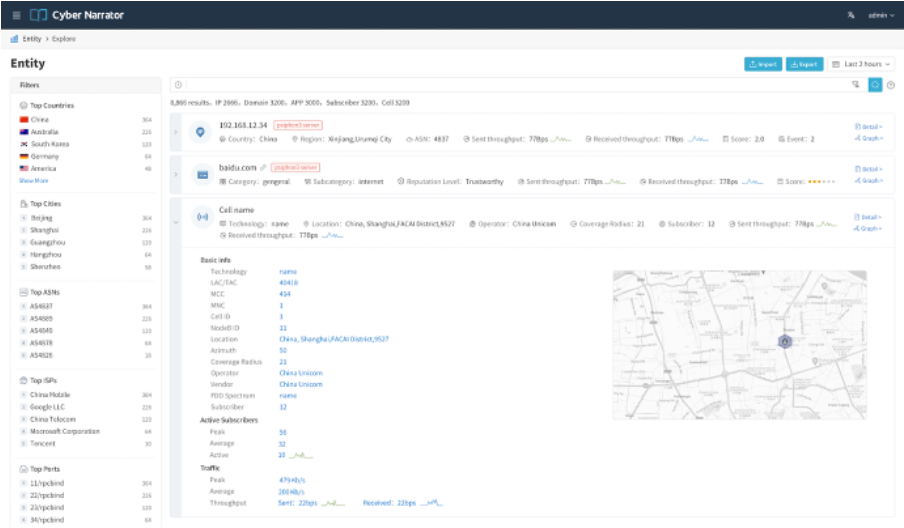
(Source: Cyber Narrator/TSG Galaxy)
Table 1: Sample of City Codes Identified Based on M22 Myanmar’s Network Planning Document
| City Code | Full Name |
| YGN | Yangon |
| NPT | Naypyidaw |
| MDY | Mandalay |
| THL | Tachilek |
| MUSE | Muse |
| MWD | Myawaddy |
(Source: Author research from Geedge database)
Geedge is public about its desire to market its products internationally. At an event in January 2024 in Hainan, co-founder Fang Binxing (方滨兴) described the company’s vision as “expanding into international markets, promoting Chinese solutions to the world, and promoting Chinese technologies globally” (辐射国际市场,把中国的方案推向世界,把中国的技术推向世界). Fang, who is often referred to as the “father of the Great Firewall” (中国防火墙之父), explicitly identified countries participating in the OBOR initiative as a key priority for this global push (Sohu, January 11, 2024).
Job advertisements posted by the company also provide evidence of the company’s international expansion. These show the that Geedge is seeking candidates “able to speak English or another foreign language with working proficiency” (可以使用英语或者其他外语作为工作语言) and willing to undertake three- to six-month assignments in countries such as Pakistan, Malaysia, Bahrain, Algeria, and India, several of which are key OBOR corridors (Zhipin, August 22; The Globe and Mail, September 8).
Geedge Provides Capabilities, Clients Set Censorship Parameters
A striking feature exposed by the leak is the degree of operational control delegated to foreign government clients. Rather than forcing foreign operators to rely entirely on Geedge engineers for rule updates and block lists, the company provides a client-side interface, sometimes referred to as “AppSketch Works.” Internal documents describe it as a management application through which local staff can define and maintain curated sets of VPNs and circumvention tools to be whitelisted or blocked. [5] This interface layer lowers the technical threshold for sophisticated censorship while the underlying DPI system remains proprietary and centrally updated by Geedge remotely from the PRC.
Figure 2: Screenshot of Appsketch
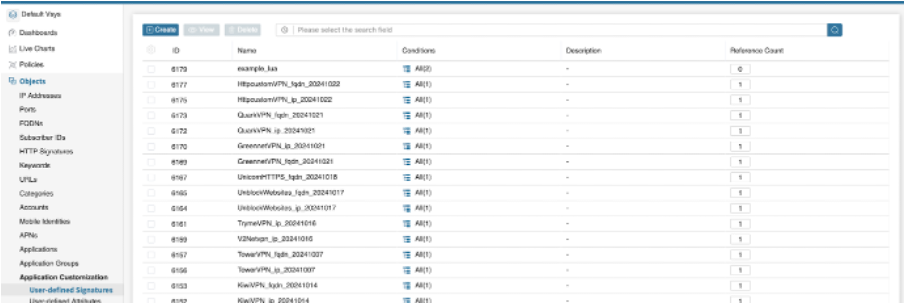
(Source: AppSketch)
Geedge also maintains a shared, cross-border database of VPN, proxy, and bridge nodes compiled from all deployments of its products around the world. This allows a circumvention endpoint exposed in one country to be added to block lists elsewhere almost immediately, effectively turning each customer into both a consumer and a contributor to a global censorship threat-intelligence pool centered on PRC-developed infrastructure (InterSecLab, September 9).
Geedge’s products do not rely exclusively on proprietary code. They often use existing commercial software development kits (SDKs) and open-source components, including well-known traffic analysis and visualization tools. In many cases, these libraries appear to be repurposed for mass surveillance, censorship, and data exploitation rather than their intended analytic functions. This lowers development costs and accelerates feature updates. But it also raises legal and ethical concerns. Upstream vendors and maintainers may not be aware that their work is being embedded in repressive systems, and it is unlikely that they would support such use cases. No attempts have been made, however, to anticipate or prevent the use of these tools for repressive ends.
Table 2: Open-Source and Commercial Tools Used by Geedge
| Technology | Category |
| Apache Ecosystem (Kafka, Flink, Spark), Gohangout | Big Data and Stream Processing |
| ClickHouse, ArangoDB, Redis, MariaDB, MySQL | Database |
| Docker, Kubernetes | Container |
| ZooKeeper | Coordination & Configuration |
| Prometheus, Grafana | Monitoring & Observability |
(Source: Geedge leak)
Digital Silk Road Cooperation Part of Beijing’s Strategic Planning
In strategic policy documents, Beijing frames the export of its Internet governance system as part of its national strategy. Since the 14th Five-Year Plan period, the PRC has tied digital infrastructure, cyber security, and data governance to its ultimate goal of “national rejuvenation” (伟大复兴), calling for “digital sovereignty” (数字中国), and the need to become a “network great power” (网络强国) (PRC State Council, December 28, 2021). Early commentary on the upcoming 15th Five-Year Plan emphasizes both self-reliance in core technologies and deeper technological cooperation with OBOR partners (PRC State Council, October 28; China Brief, November 3). The recommendations for the upcoming 15th Five-Year Plans and the “High-Quality Belt and Road Cooperation: Partnership on Connectivity” document issued by the Ministry of Foreign Affairs (MFA) identify digital infrastructure, data governance, and “network security” as priority areas for cooperation and OBOR engagement (MFA, October 17, 2023).
These documents formalize and promote partnerships for the co-development of standards and platforms to strengthen network sovereignty and manage cross-border data flows. Within this framework, the Geedge–MESA systems deployed in Myanmar, Pakistan, and other OBOR states operationalize the vision of the Digital Silk Road by embedding PRC-developed surveillance and censorship capabilities into the core infrastructure of partner countries.
On-the-Ground Reception and Reactions
Local reporting reveals unease regarding the implementation of these systems. In Myanmar, work by the covert activist group Justice For Myanmar and the U.K.‑based investigative journalism organization Finance Uncovered have reported sharp criticism from civil society over the use of Chinese-built censorship platforms, including Tiangou Secure Gateway, by the post-coup military junta (Finance Uncovered, May 21; Justice For Myanmar, September 9). This technology enables authorities to directly target activists, journalists, and dissidents. Although there is as yet no direct evidence that Geedge’s technology has been used for these purposes, the growing capacity to do so signals risks for personal safety and the closure of civic space.
In Pakistan, a censorship and traffic surveillance platform has been installed at key Internet and telecommunications chokepoints since 2023. Known as Web Monitoring System 2.0 (WMS 2.0), it is based on Geedge technology and enables authorities to block content and monitor user behavior in near-real time. It is currently moving toward a centrally managed, scalable “national firewall” that is comparable in both architecture and effect to the PRC’s Great Firewall. Human rights defenders, journalists, and civil society organizations within Pakistan and elsewhere have voiced concern over the system’s lack of meaningful safeguards against overreach or abuse, and its capacity to defeat core anonymity tools (Amnesty International, September 9).
Figure 3: Flowchart of Technology Implementation
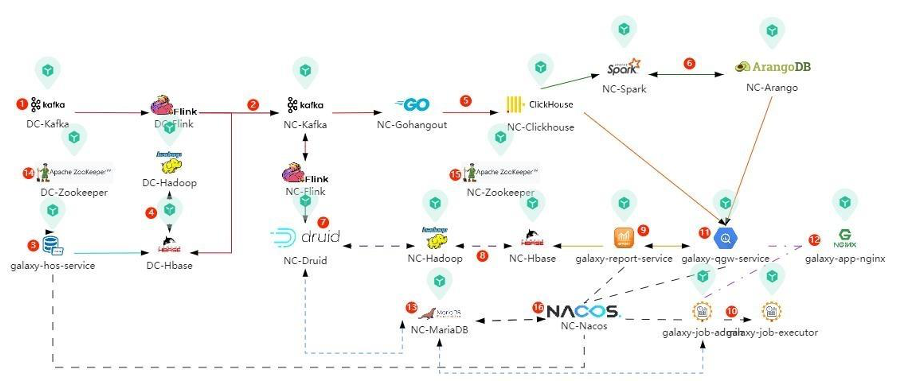
(Source: Geedge Leak)
Conclusion
The Geedge and MESA materials shed a partial light on how the PRC’s censorship-as-a-service model is marketed and deployed overseas. While the technical documentation is substantial, however, the leak contains limited information on pricing, contractual terms, making the exact mechanics of its commercial operations unclear. The leak also does not contain evidence of explicit state directives. Although Geedge is closely coupled to the MESA Lab under CAS, with which it shares research outputs and whose code bases point to joint development of core algorithms, the lack of direct state involvement reinforces the ambiguity of Geedge’s status as a “private” vendor. The line between state research and commercialization thus appears largely bureaucratic, not functional. This pattern echoes the relationship revealed in the iS00n disclosures, where a nominally private cybersecurity contractor conducted offensive operations against foreign telecoms, ministries, and financial institutions on behalf of PRC public security and intelligence clients.
Geedge’s implicit sanction by the state, through its work with government-run entities, puts its work on a continuum in the PRC’s digital strategy. This continuum runs from AI-enabled offensive operations as highlighted in the Anthropic report to the active shaping of international technical and legal norms of information control through the export of commercial digital censorship tools. The goal throughout is to further consolidate Beijing’s global power and influence.
Notes
[1] Note that the “Great Firewall” is an umbrella term for a series of Internet censorship systems (see Great Firewall Report, accessed December 3).
[2] MESA stands for Massive Effective Stream Analysis.
[3] Beijing is also externalizing its governance model in domains beyond cyber, such as public security and police work (Carnegie Endowment for International Peace, November 13).
[4] Feng Yang. “The tale of deep packet inspection in China: Mind the gap.” 2015 3rd International Conference on Information and Communication Technology (ICoICT). Nusa Dua, Bali, Indonesia, 2015, p. 348-351; Li Li. “Advancing Obfuscation Strategies to Counter China’s Great Firewall: A Technical and Policy Perspective.” arXiv, 2025, arXiv:2503.02018v1.
[5] These include a set of over 30 VPN tools with detailed blocking strategies (~yinjiangyi/VPN封堵需求.html), a VPN whitelist feature introduction (Galaxy Release 21.12 (21 Dec 2021).html), and a VPN whitelist recommendation program (OLAP 22.02 Upgrade Notes.html).


