
The New Issue of Technical Mujahid, a Training Manual for Jihadis
Publication: Terrorism Monitor Volume: 5 Issue: 6
By:
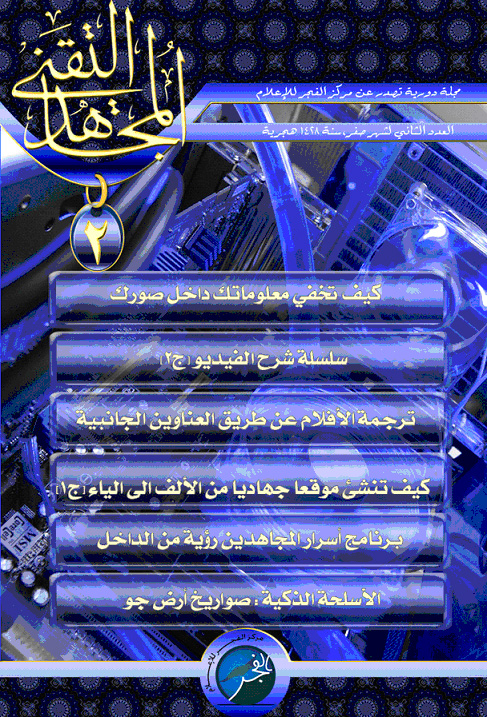
The al-Fajr Information Center, a jihadi organization, recently published the February 2007 issue of Technical Mujahid, a magazine released once every two months that is available online. The release marks the second issue of the publication. The various jihadi websites have posted links to different locations to download the publication, that way stifling any attempts by outside forces to remove the document from the web (https://www.arabteam2000-forum.com, March 13). According to the editor-in-chief of Technical Mujahid, Abu al-Mothanna al-Najdi, the objectives of the magazine are to eradicate the phobia and anxiety suffered by those who refrain from participating in jihad because they erroneously believe that intelligence services are monitoring their every move. Additionally, the publication aims to spread a sense of security, vigilance and self-confidence, in a scientific way, among members of jihadi forums by educating them in jihadi propaganda and enhancing their knowledge of field operations. To achieve these objectives, the magazine is organized into six sections of technical training that are aimed at helping the mujahideen carry out certain tasks.
Section 1: Covert Communications and Hiding Secrets Inside Images
Secure communications, a significant and important tool for any underground group, is the first training subject in the magazine, authored by Abi Musab al-Jazayri, “the Algerian.” After a brief historical account of the evolution of secret communications from the use of secret ink to Morse code to binary 256 bit and 2048 bit encoding, al-Jazayri launches into the body of his training article with “the thing that scares the FBI most is the use of secret communication techniques, by jihadis, known as the concealment science.” The training article outlines steganography, which is the art of hidden messages; steganalysis, the art of detecting hidden messages; and the merits of hiding data in innocuous-looking images. Al-Jazayri appears to be an expert on the subject judging from the details he included such as image pixels, mathematical equations to prevent distortions in pictures used to hide data and the disadvantages of encryption software available on the market like Ezstego, S-Tools and Hide and Seek, which can all be easily deciphered using hexadecimal editors. He explains that a good program to use is the “Secrets of the Mujahideen” software application because it is a dual system that hides encrypted data in a picture and compresses the files to nullify steganalysis methods. He then provided an example of hiding 20 communiqués of the Islamic Army in Iraq in a 100 x 50 pixel picture. His example highlights the necessity of applying steganalysis before choosing a picture to hide data. Al-Jazayri concludes the training by warning jihadis not to use ineffective encryption programs in their secret communications, reiterating that the best encryption uses multiple concealment techniques such as compression, encoding and concealment or uses communication-engineering techniques such as Spread Spectrum.
Section 2: Designing Jihadi Websites from A-Z
The second section, prepared by Abu Dojaina al-Makki, simply explains the steps of designing websites and uploading them to the internet via a host company. There is nothing unusual about this training except that the writer recommends hiring foreign website host companies because Arabic companies are incompetent, have “attitude” problems and break down frequently. To jihadis, experience in website development is important since the web is one of their key communication venues across various theaters of conflict. It also provides a recruitment opportunity for jihadi operations.
Section 3: Smart Weapons, Short Range Shoulder-Fired Missiles
The training magazine recommends two types of short range shoulder-fired missiles for the jihadis as the most appropriate anti-aircraft weapons: the U.S.-made Stinger and the Russian-made Igla missiles. Abi al-Harith al-Dilaimi, the writer of the smart weapons section, included many details about the specifications of the missiles, operating manuals and the electronic heat-seeking control systems of the missiles. The section is very thorough and even includes pictorial illustrations. Al-Dilaimi does not fail to brag about the recent downing of U.S. aircraft using these missiles, saying “The best example we can give about these missiles is the downing of 10 helicopters in one month in Iraq such as the Apache, Black Hawk, Chinook and even an F-16 supersonic fighter jet that was shot down in al-Karma area west of Baghdad by the Islamic State of Iraq mujahideen in cooperation with the Mujahideen Army on November 27, 2006.”
Furthermore, the training touches on the types of supersonic aircraft, helicopters and slow military cargo planes and missile counter-measures employed by these aircraft, such as heat flares that can throw off-course heat-seeking missiles and infrared missile repelling systems. The Russian-made Igla is an exception as it has a Nitrogen-cooled heat seeking system capable of resisting the heat flares and identifying the real target among the decoy targets. The section also includes Igla and Stinger specification lists and a table of the English equivalents of the technical terms used in Arabic. Al-Dilaimi ends the training with a note saying, “we would like to assert that the mujahideen have proven skillful use of these weaponry by inflicting heavy loses on the colonizing U.S. forces in Iraq and Afghanistan.”
Section 4: The Secrets of the Mujahideen, an Inside Perspective
Also mentioned in other jihadi publications, the “Secrets of the Mujahideen” is a computer program for internet communications. According to the security section of the Global Islamic Media Front, who wrote this training section, it is the first Islamic encryption software. The section on the program affirms the necessity of creating Islamic encryption tools due to the currently ineffective programs available on the market. In general, the section talks about the following five topics: 1) encryption and correspondence through the internet; 2) encrypting personal emails; 3) the degree of encryption and the symmetric, 128 bit, and asymmetric, 1024 bit, encryption keys; 4) public encryption keys and pass phrases that protect them; and 5) private encryption keys and decryption keys.
The authors claim that the Secrets of the Mujahideen program offers the highest level of encryption in asymmetric encoding that furnishes safe transfer of public encryption keys over the internet. The keys, which use “key prints” to identify the recipient, can be advertised in the jihadi forums. In general, the strength of the jihadi encryption program lies in the following: the use of the best five algorithms in encryption science; strong symmetric encryption; private and public asymmetric 2048 bit keys; strong compression of data; use of stealthy encryption keys and algorithms; secure deletion of files, elimination of retrieval possibilities; and the ability to run it from a flash disc, i.e. the program does not have to run from a computer hard drive. The encryption training section is extremely detailed and explains all the technical implications of the program. The writers claim that the program surpasses all international symmetric encryption systems.
Section 5-6: Video Technology and Subtitling Video Clips
This is the second lesson in a series of training that will be included in future issues of the magazine. Although very technical, there is nothing unusual about the video training as it talks about signal reception, sample rates and vertical video samples. In the same context, the training explains how to dub video clips with subtitles and background voiceovers. Video skills are clearly needed by jihadis for their propaganda campaigns. One well known example would be the videos released of the “Baghdad Sniper” (Terrorism Focus, February 14). Abu al-Hassan al-Magribi, the writer of this section, concludes by stressing the importance of translating jihadi propaganda into as many foreign languages as possible.
The Conclusion of the Magazine
The editor-in-chief ends the magazine with an article calling upon jihadi forum participants to contribute technical information to the magazine, saying “Haven’t you thought that you might have some knowledge that would assist your brothers in our nascent Islamic state of Iraq? My technical jihadi brother, this magazine gives you the opportunity to share whatever scientific knowledge you have with tens of thousands of jihadis frequenting the Islamic forums. Half of the efforts we exert in our battles against enemies of God occupying our land in Iraq, Palestine, Chechnya and Somalia lie in the media that will enlighten our fellow Muslims with facts about the crusaders.” He reminds the readers of the al-Qaeda in Iraq leader Abu Hamza al-Muhajir’s call to Muslim scholars and scientists to utilize their knowledge for the benefit of jihad. Finally, the magazine instructs willing participants to send their technical articles to https://www.teqanymag.arabform.com. That website contains a welcoming note from the board of editors of the magazine and a contact form where participants can send in their technical articles.
The next issue of Technical Mujahid is set to contain the following subjects: jihadi forums and secure surfing on the internet; smart weapons such as night vision and thermal imaging; and information on how intelligence agencies can bug cellular phones. Also, al-Fajr Information Center has announced the release of an interview with a jihadi leader in Afghanistan that will be posted soon. Clearly, the Technical Mujahid is not a magazine for the common jihadi since it contains many scientific details. To comprehend and apply the training the magazine offers, the jihadi has to have a certain level of education and specific academic background or be tutored by an expert in training camps or safe houses. Nevertheless, it is another example of how the internet is used to train fellow mujahideen in topics ranging from weapons training to secure communications.




